Setting access policies
To change the access policy settings, in the navigation menu, click Manage > Security Policies, and then click the Access policy tab.
Contents
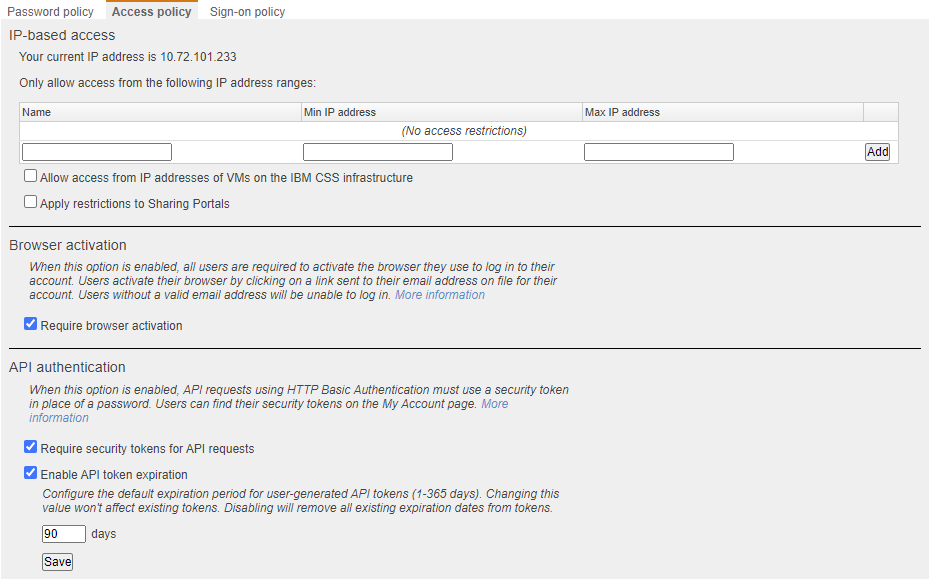
IP-based access
IP-based access blocks traffic to Kyndryl Cloud Uplift from all IP addresses outside of a designated range. For example, you may want to limit access for your customer account to IP addresses in the company network.
To enable IP-based access
- Create a name for this access policy.
-
Set the range of IP addresses that is allowed.
Notes- Both minimum and maximum addresses are included in the range of allowed addresses.
- Make sure all of the IP addresses you use are in the list of allowed addresses. You may have multiple IP addresses if you use a VPN, or if you have a firewall rule that directs different types of network traffic out of different end points.
- SRA access may be blocked in Microsoft Azure regions if IP-based access is enabled.
- Click Add. IP addresses within this range are permitted to access the account.
- You can use the following options to modify your access restrictions:
- Allow access from IP addresses of VMs on the Kyndryl Cloud Uplift infrastructure – Automatically allows access to Kyndryl Cloud Uplift from VMs running in Kyndryl Cloud Uplift. This permits users to access their Kyndryl Cloud Uplift assets from the VM.
- Apply restrictions to Sharing Portals – Permits only IP addresses within the specified IP address ranges to access Kyndryl Cloud Uplift environments using sharing portal connections generated from a sharing portal.
Browser activation
Browser activation lets administrators create an additional security layer by requiring users to verify their accounts before they can sign in from an unregistered browser. When enabled, all users see this screen when they sign in from an unregistered browser:
Browser activation is required by default.
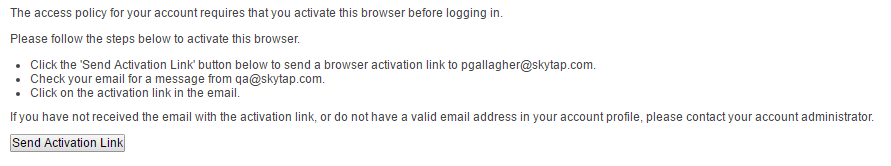
When a user clicks Send Activation Link, an activation email is sent to the address associated with that user account. When the user clicks the activation link in the email, the user must enter a valid password; afterward, the browser is activated (via a saved cookie) and is ‘trusted’ by the customer account.
Users who don’t have a valid email address in their profile never see the activation email and won’t be able to sign in to their accounts. Those users should contact their administrator to update their email address, which automatically sends an email validation link (to find your account administrator, see Finding your primary administrator).
For new users, clicking on the initial user activation link also activates their default browser.
API access
To enable security tokens for API access
-
Click Require security tokens for API requests to enable API security tokens for users.
When this feature is enabled:
- Users can generate unique security tokens to access Kyndryl Cloud Uplift using the REST API.
- Users must use their API security token to authenticate API requests. The API won’t accept requests that are authenticated with the user’s account password.
- Users can view and regenerate their security tokens from the My Account page. For instructions, see Finding your user name and API security token.
-
Admins can delete user security tokens from the Edit User page (accessed from the Users page on the Admin panel).
Notes
- We strongly recommend that you require security tokens for API access. If this feature is disabled, users can authenticate to the API using their standard user name and password.
- API security tokens are more secure than password-based authentication.
- API security tokens are difficult to guess and can be changed independently of account passwords.
- For more information about the API, see Kyndryl Cloud Uplift REST API.
-
Optionally, click Enable API token expiration to set new API tokens to automatically expire after the number of days you specify.
Notes
- Enabling this setting changes the token expiration time for all users.
- By default, API tokens for new accounts automatically expire after 90 days for all new Kyndryl Cloud Uplift accounts.
